Today is the day! — Nitrux 3.5.0 “cx” is available to download
We are pleased to announce the launch of Nitrux 3.5.0. This new version combines the latest software updates, bug fixes, performance improvements, and ready-to-use hardware support.
Nitrux 3.5.0 is available immediately.
🔰 Information: The codename for this release is “cx,” which reflects the extensive updates, new additions, and security enhancements that collectively expand and strengthen the overall distribution.
⚠️ Important: Despite the efforts and improvements in this and previous releases, we’re not claiming to be security or forensic experts or that the distribution is “impenetrable” or “unhackable,” so there isn’t any misunderstanding. Suggestions to continue improving on this area are welcome at our organization at GitHub (open a new discussion).
🔰 Information: The ISO file is signed with a GPG key, and we only provide SHA512 checksum files; please check the Notes to know more.
This release is brought to you by our friends at Packagecloud. Packagecloud provides Nitrux Latinoamericana with the vital infrastructure that allows us to build our distribution.
Lightning-fast, secure, automated package management.
Consider sponsoring Nitrux at Open Collective or Ko-fi. By sponsoring Nitrux, you give the development team a regular and predictable income to cover our hosting, development, and hardware testing costs.
📜 Table of Contents
✨ What’s new
We recommend new users do a fresh installation using the latest media. For users of the previous version (3.4.1), please check the Notes for information about upgrading Nitrux.
Nitrux 3.5.0 build.310524.cx uses Linux 6.8.12-1 (Liquorix)
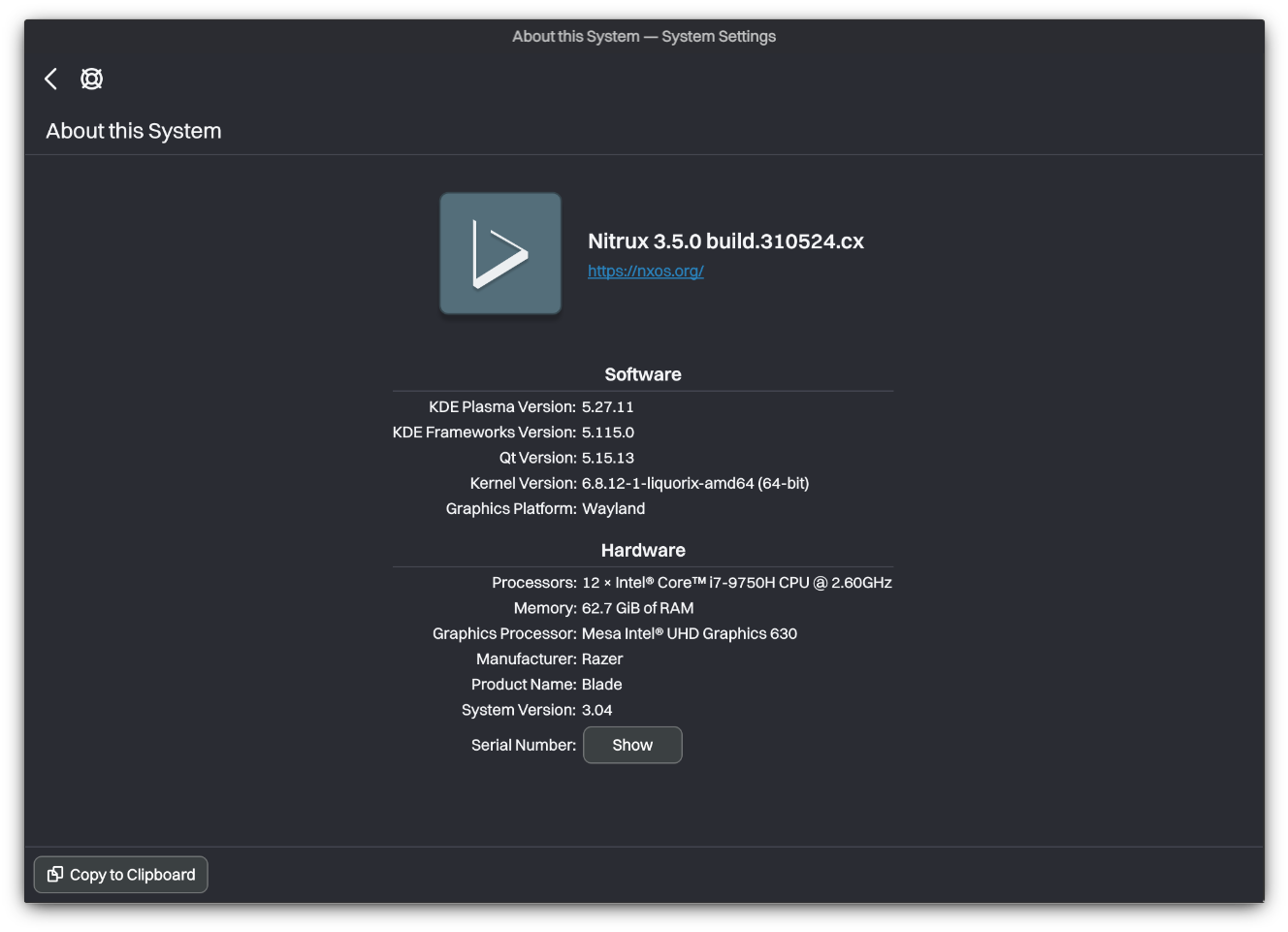
We’ve updated the distribution components listed below.
- Firefox to version 126.0.1.
- KDE Plasma to version 5.27.11, KDE Frameworks to version 5.115.0, and Qt to version 5.15.13.
- NVIDIA Linux x64 (AMD64/EM64T) Display Driver to version 555.42.02.
- We have updated our linux-firmware package to include newer files from the Linux firmware repository (up to the commit b9d2bf23) for the following drivers.
- “airoha”: Bluetooth devices with Airoha chips.
- “amdgpu”: Open-source graphics driver for AMD Radeon GPUs.
- “ath3k”: Atheros AR3000 series Bluetooth chips.
- “brcm”: Broadcom wireless and Bluetooth devices.
- “cirrus”: Cirrus Logic video cards.
- “iwlwifi”: Intel Wireless Wi-Fi Link adapters.
- “mediatek”: MediaTek SoC firmware.
- “qat_4xxx”: Intel QuickAssist Technology 4xxx series accelerators.
- “tsse_firmware”: Firmware for TSSE devices for enhanced security and encryption capabilities.
- Nitrux Update Tool System to version 2.1.4.
- Our OpenRC configuration now includes a new runlevel called “async.” This runlevel aims to defer the initialization of non-essential services to a runlevel that starts in parallel with the default runlevel, thus improving boot time. Additionally, we include a new service script to start the NTPSec NTP server.
- The Luv icon theme now includes an icon for CoreCtrl, an updated icon for the NVIDIA X11 settings application, and an icon for the screen configuration system tray item in our Plasma theme.
- We have updated our zswap configuration to use Z Standard (zstd) as the compression algorithm and zsmalloc as the memory pool allocator.
- Our Sysctl settings have been updated for better security and increased performance. These changes include:
- Enable BPF JIT hardening if the JIT is enabled: Enabling hardening for the Berkeley Packet Filter (BPF) Just-in-time (JIT) compiler aids in mitigating JIT spraying attacks.
- Reduced memory compaction overhead: Reduce CPU overhead and improve overall system responsiveness, especially in memory-intensive applications leading to more stable performance by avoiding sudden spikes in CPU usage caused by proactive compaction.
- Improve performance in contended lock scenarios: By allowing more aggressive page locking, we improve performance in scenarios with contention for memory pages, which can occur in applications with high memory usage and multi-threaded environments.
- AMD Open Source Driver for Vulkan® to version v-2024.Q2.1.
- XWayland to version 24.1.0.
- MESA 3D Graphics Library to version 24.1.0.
- Restore the previously used powerlevel10k configuration using the “Lean” style instead of “Pure” for the ZSH shell.
- Distrobox to version 1.7.2.1.
We’ve added the following components to the distribution.
- The following Maui Apps (version 3.1.0) are now included as AppImages.
- Bonsai.
- Buho.
- Clip.
- Nota.
- Pix.
- Shelf.
- Strike.
- VVave.
- The following non-Maui Apps are now included as AppImages.
- NX Software Center, which includes the fixes for the issues listed below.
- To continue improving the security of our distribution, we added the following changes.
- Fill freed pages and heap objects with zeroes: Ensure that when freed, they are filled with zeroes, enhancing security by preventing data leaks through uninitialized memory.
- Disable merging of slabs of similar sizes: Preventing the kernel from merging memory slabs of similar sizes can improve security by making it harder for attackers to exploit specific memory corruption vulnerabilities.
- Enable Redzoning: Redzoning adds extra areas around memory slabs to detect overflows by checking if a slab is overwritten past its actual size. This helps detect buffer overflows.
- Disable Virtual Syscalls: Disables virtual Syscalls and system calls implemented in user space for performance reasons, potentially reducing the attack surface for specific exploits.
- Randomize kernel stack offset on syscall entry: Introduce randomness to the kernel stack offset whenever a system call is made, adding another layer of security by making it harder for attackers to predict memory addresses.
- We have added a new service script for OpenRC to use the early OOM killer program nohang desktop configuration (instead of the default) since it provides settings optimized for desktop usage.
- CoreCtrl. CoreCtrl is a free and open-source GNU/Linux application that allows you to control your computer hardware easily using application profiles. It aims to be flexible, comfortable, and accessible to regular users.
- 🔰 Information: Check out its wiki to learn more about using it to manage AMD CPUs and GPUs.
- 🔰 Information: NVIDIA users can download GreenWithEnvy from Flathub for a similar application; see our tutorial about software management.
- We have added udev rules and a kernel parameter to turn off USB auto-suspend.
- We have added clinfo and wayland-utils to display information about OpenCL and Wayland in KInfoCenter.
- 🔰 Information: KInfoCenter is hidden by default but can be used by running the command kinfocenter.
- We have added a service script for OpenRC to make the following changes to improve gaming performance specifically:
- Enable THP (Transparent Hugepages) for all memory locations: Improve performance for applications with large memory usage and access patterns that benefit from larger pages.
- Disable memory page fragmentation: For workloads like gaming, it can provide benefits such as reduced CPU overhead, improved system responsiveness, and more predictable performance.
- xpadneo, an Advanced Linux Driver for Xbox One Wireless Controller (shipped with Xbox One S).
- xone, a Linux kernel driver for Xbox One and Xbox Series X|S accessories. It is a modern replacement for xpad, aiming to be compatible with Microsoft’s Game Input Protocol (GIP).
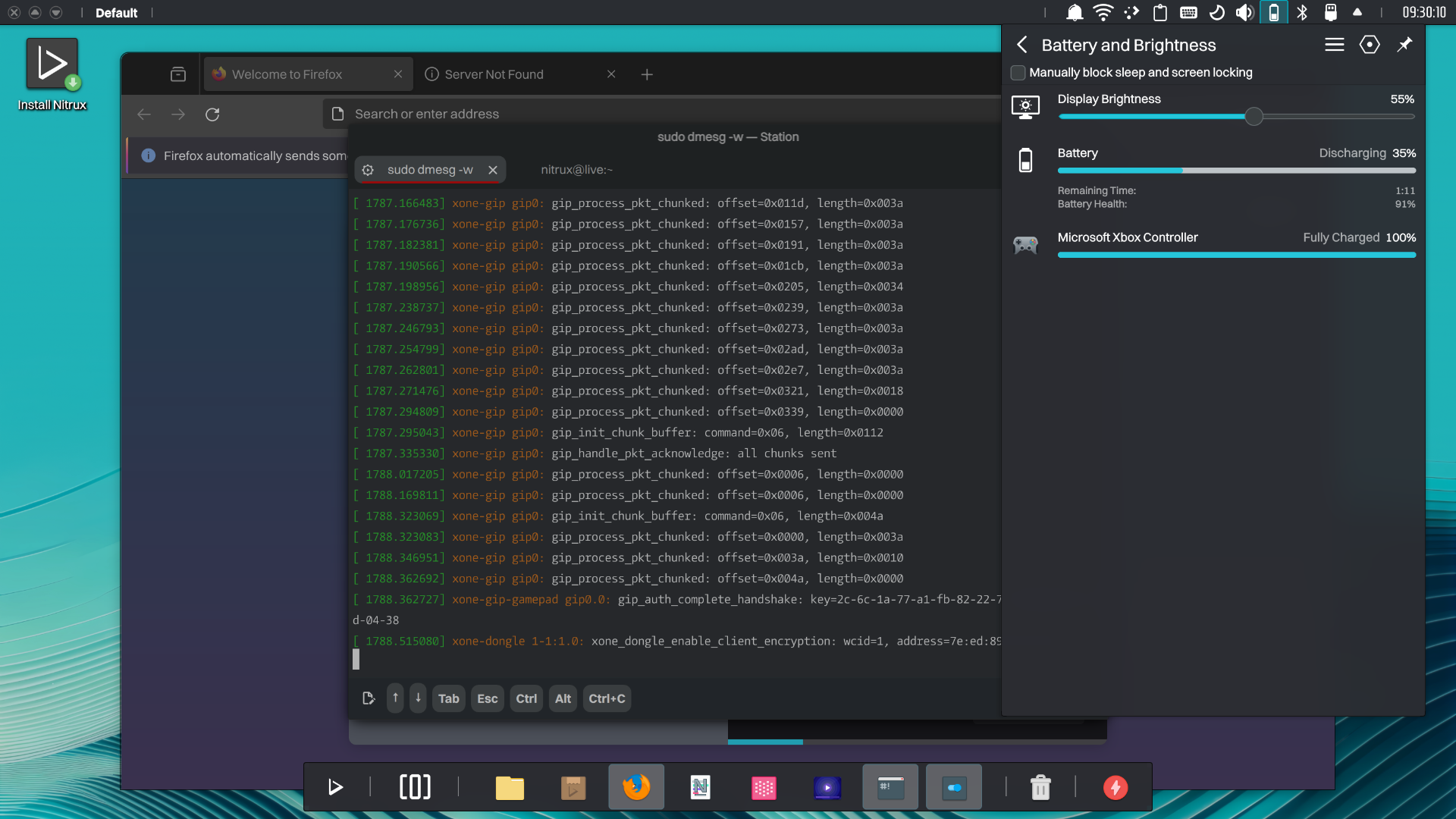
-
- 🔰 Information: To use a wireless Xbox One dongle with this driver, first connect to the internet, then run the following command to download the required firmware, then plug the dongle and pair the controller.
- ⚠️ Important: The script file below creates files in the root directory; see XFS Features and Root Immutability in Nitrux.
- ⚠️ Important: The script file below creates files in the root directory; see XFS Features and Root Immutability in Nitrux.
- 🔰 Information: To use a wireless Xbox One dongle with this driver, first connect to the internet, then run the following command to download the required firmware, then plug the dongle and pair the controller.
sudo /usr/local/bin/xone-get-firmware.sh
We’ve fixed or closed the following issues in the distribution; see Report bugs.
- [CLOSED] Can’t use PolicyKit authentication in Live session #167.
- [CLOSED] AppImages can’t be downloaded/installed using the NX Software Center #138.
- [CLOSED] The mouse is intermittently disconnecting in Nitrux #170.
- [CLOSED] Clicking “Remove” when highlighting an AppImage does not delete the AppImage #134.
- [CLOSED] Add service file for NTP service #168.
- [CLOSED] Gamescope does not work because of a missing library #173.
- Fix the install scripts to install Steam, Bottles, and Heroic Games Launcher.
- Fix the Fcitx5 main binary missing from the default installation.
- Fix an issue with powerlevel10k preventing the use of GPG.
We’ve removed the following components from the distribution.
- Remove the rngd service from the default runlevel in OpenRC, as it’s no longer needed for modern computers with integrated hardware random number generators.
- 🔰 Information: The service script is still available in the root directory for those who want to use it.
- Remove additional services from the default runlevel to speed up the boot time.
- 🔰 Information: All the available service scripts can be found in the directory /etc/init.d.
📥 Download
Here are various ways to download our ISOs and virtual appliances.
- ISO — Direct HTTP Download from our server.
- FOSS Torrents (Torrent).
- Sourceforge (mirror).
- OSDN (mirror).
- ⚠️ Important: We cannot add or remove ISO files from this mirror due to connectivity problems with OSDN (504 Gateway Time-out).
Check our tutorial and use the files below to verify the ISO file’s integrity and authenticity.
⛔ Known issues
To see a list of known issues, click here.
🗒 Notes
To see a list of release notes, click here.
🐞 Report bugs
To report bugs, please use our bug tracker on GitHub.
📝 Changelog history
To see a list of previous changelogs, click here for the changes archived at our site or for the changes archived at Sourceforge.
📰 Resources
Here are various articles, tutorials, and other information on our blog.
📢 PSA (Post-release service announcements)
Here’s a list of post-release service announcements for this version of Nitrux.
🚀 Get involved
Everyone can participate in the Nitrux community on many levels, from advising fellow Nitrux users to becoming a maintainer. Any contribution, even the smallest, is valued. To start contributing to Nitrux, click here.



